Why Cybersecurity Leadership Matters
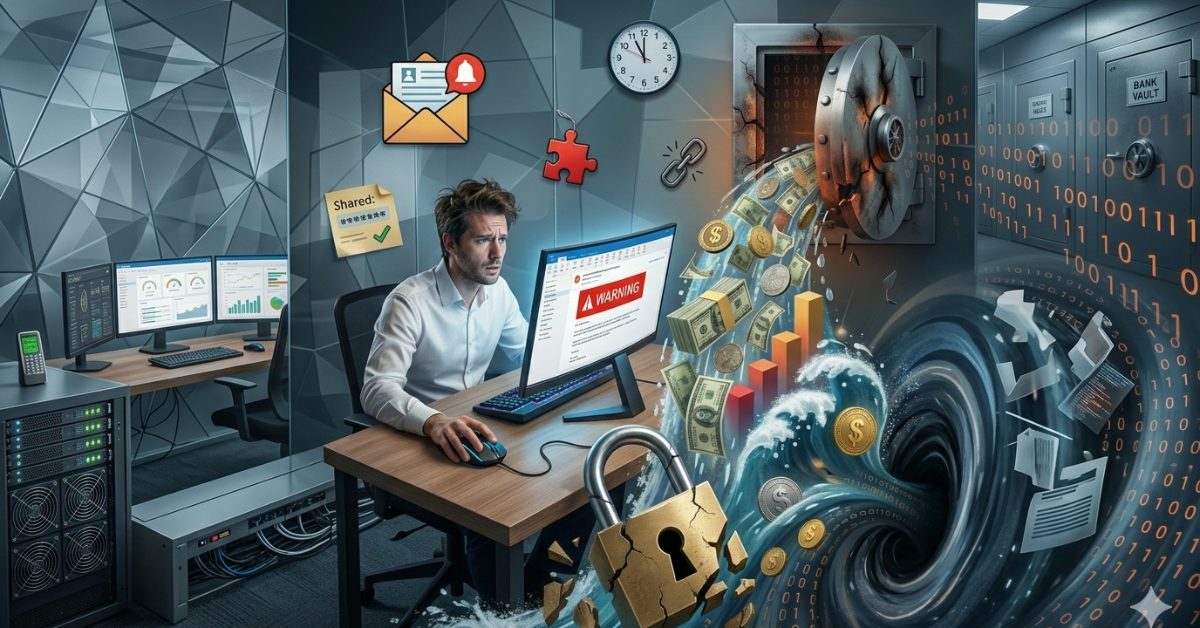
Cybersecurity leadership sets the tone for how an organization approaches digital safety. While technical controls are essential, the biggest cybersecurity risk often comes from human behavior—mistakes like clicking malicious links or bypassing protocols. An effective leadership approach to cybersecurity risk means going beyond simplistic warnings. Leaders must create structure, set expectations, and enforce accountability. Only through this governance-focused lens does the organization build a culture where employees pause, verify independently, and treat security as non-negotiable.
If you’re ready to take action and build a behavior-based security culture, Gallop Technology Group is here to guide you. We can assist you with executive cybersecurity strategy, governance frameworks, and training designed for small businesses. Our tailored services help you implement enforceable policies, incident readiness planning, and access control that mitigate human error and build real resilience. Call our team at 480-614 4227 and get your free IT assessment today.
How Leadership Reduces Cybersecurity Risk at the Top
Organizations often treat cybersecurity as a technical problem, placing the responsibility solely on IT. But cybercriminals exploit human behavior, not just systems. Phishing attacks, for example, succeed because someone clicks. Leaders play a critical role in reducing cybersecurity risk by building an environment where secure behavior is expected, modeled, and enforced.
A leadership approach to cybersecurity risk transforms casual guidance—“be careful online”—into structured oversight. When executives prioritize cybersecurity governance, it becomes part of organizational DNA. Behavior is guided not by fear, but by consistency. Control is enacted not by technology alone, but by people and processes.
Pillars of Effective Executive Cyber Security
Policy and Accountability
Creating enforceable policies is critical. Leadership must define acceptable behavior, consequences for violations, and review cycles. Whether you have in-house IT or outsource it, policies provide the framework for compliance.
Structured Training
Stand-alone training sessions aren’t enough. Leadership must ensure continuous education, focusing on real-world scenarios and behavioral reinforcement. Employees need to internalize the motto: if money, sensitivity, or urgency are involved—pause and verify independently.
Access Control and Governance
Limiting access prevents human errors. A true leadership approach to cybersecurity risk ensures employees only have permissions they need. Governance isn’t a one-time checklist but a living system of permissions, checks, and audits.
Discipline and Modeling Behavior
Security virtues can’t be optional. When leaders model careful password management or verification habits, it sends a powerful signal. If executives are careless, employees assume it’s safe. Conversely, when leaders take secure behavior seriously, it becomes normative.
Incident Planning and Readiness
Technical teams may build firewalls and backups, but leadership ensures responsibility is assigned during an incident. Incident planning clarifies who calls the shots, when to bring in external partners, and what communication is needed. This governance preparation makes responses more effective—and faster.
Executive Cyber Security in Action: Real-World Impact
A great example of behavior-focused cybersecurity leadership comes from a multinational firm that instituted a rule: “If you receive a money request, pause and verify verbally.” Leadership modeled this by always confirming before approving transactions. Result? A 40% drop in fraudulent payment incidents within a year. This demonstrates just how powerful influencing human behavior can be when leadership leads by example.
Governance Over Technology: A Leadership Mandate
Cybersecurity today is governance. Executives need not be technical experts, but they must enforce the rules. Here’s why this shift in focus matters:
- Behavior is trainable. Mistakes happen—but can be greatly reduced through consistent behavioral modeling and enforced standards.
- Processes are controllable. Leadership designs the “pause-and-verify” step into every process involving money or sensitive data. That oversight saves organizations from costly breaches.
- Human risk is manageable. We cannot eliminate every threat, but we can significantly reduce human error. With governance and accountability, that error becomes a controlled business risk.
Leaders must treat human behavior as a key vulnerability—but also a strength. Over time, careful habits become habitual.
The “Pause, Verify, Model” Leadership Triad
Leaders wield three simple but powerful behaviors to shape culture:
- Pause: When urgency arises—especially around money or sensitive data—require a moment of verification.
- Verify: Always use an independent source—call a trusted contact, check through different channels, or inspect logs.
- Model: Demonstrate these behaviors publicly. When executives pause before approving, employees learn: this matters and serves as a standard.
This triad may sound basic, but it creates measurable impact. It gives staff clear actions: “When this happens, I do that.”
True Stories from Executive Cybersecurity Strategy
Several organizations that embraced behavioral risk governance saw immediate results:
- One nonprofit trimmed incident volume in half after leadership called for policy-based verification steps.
- A manufacturing firm restructured payment procedures, requiring manager approval for changes in banking info; fraudulent transfers fell to zero.
- A financial services company tied employee performance reviews to security training participation—click rates on phishing tests dropped 60%.
Each of these examples demonstrates how executive cyber security efforts, when structured and enforced, directly reduce risk.

Common Objections and Leadership Responses
- “I’m not technical.” You don’t need to be. Leadership is about structure and consistency—not running scans or managing firewalls.
- “This slows business down.” Yes—but slower processes that prevent breaches save orders of magnitude more time and money.
- “Our staff knows better.” People make mistakes when busy or stressed. Leading with accountability keeps best intentions from causing breaches.
- “Tech will handle it.” Firewalls and antivirus miss social-engineering and human error. Behavior-based oversight catches gaps technical systems leave behind.
Getting Started: Leadership Today
To activate executive cybersecurity governance, begin here:
- Create policy expectations clarifying verification steps
- Build behavior-based training tied to real-world scenarios
- Audit and sign-off on access and permissions
- Incorporate cybersecurity accountability into performance reviews
- Hold leaders to the “pause, verify, model” standard publicly
- Test incident plans quarterly and review them with staff
These steps form a sustainable leadership approach to cybersecurity risk.
Why Leadership Is Your Strongest Cybersecurity Defense
Cybersecurity challenges aren’t just technical—they’re human. And behavior-focused governance is one of the most practical leadership actions you can take. By implementing enforceable policies, structured training, access controls, and incident planning, executive leadership transforms cybersecurity from a vague IT checkbox into tangible business protection.
Gallop Technology Group supports small businesses in building this governance backbone. We help leaders translate strategy into structure, enforce discipline without friction, and model secure behavior so it becomes part of daily operations. If you’re ready to master executive cyber security, call our team at 480-614 4227. Partner with us to make leadership your strongest cybersecurity asset.
Sources
- Tejay & Winkfield, “Does Leadership Approach Matter? Examining Behavioral Influences…” Information Systems Frontiers (2025). https://link.springer.com/article/10.1007/s10796-025-10592-4 [link.springer.com]
- Schaltegger et al., “Human behavior in cybersecurity…” Journal of Risk Research (2025). https://doi.org/10.1080/13669877.2025.2539109 [tandfonline.com]
- Triplett, “Addressing Human Factors in Cybersecurity Leadership” J. Cybersecur. Priv. (2022). https://www.mdpi.com/2624-800X/2/3/29 [mdpi.com]
- Gartner-sourced article, “Cybersecurity Leadership… effective governance” (2025). https://sparkmoor.com/theroleofleadershipincybersecuritygovernance/ [sparkmoor.com]

Frequently Asked Questions:
Why is cybersecurity leadership more important than technology alone?
Technology can block many threats, but most successful cyber incidents begin with human behavior, such as clicking a malicious link or responding to a fake request. Cybersecurity leadership matters because leaders shape expectations, policies, and accountability. When leadership sets clear rules, models secure behavior, and enforces processes, employees follow those patterns. This governance approach addresses risks that technology alone cannot.
What does executive cybersecurity responsibility actually look like?
Executive cyber security does not require technical expertise. It means creating structure through enforceable policies, approved workflows, access controls, and incident planning. Leadership responsibility includes deciding how sensitive actions are verified, who is accountable during an incident, and how security expectations are reinforced across the organization. Executives lead by setting standards and ensuring they are followed consistently.
How does leadership reduce cybersecurity risk related to human behavior?
Leadership reduces cybersecurity risk by making secure behavior part of daily operations. When leaders require verification for urgent or sensitive requests and follow those same rules themselves, employees adopt the behavior naturally. Training, reinforcement, and visible accountability help turn security awareness into secure habits. Over time, this reduces mistakes without creating fear or friction.
Can small businesses realistically manage behavioral cybersecurity risk?
Yes. Human risk is one of the most manageable risks because behavior can be trained and processes can be controlled. Small businesses are often more agile, which makes it easier to enforce verification steps, limit system access, and clearly define accountability. A leadership approach to cybersecurity risk allows smaller organizations to build strong protection without complex or expensive tools.
How can GallopTech Group support cybersecurity leadership efforts?
GallopTech Group works with small business leaders to translate cybersecurity strategy into practical governance. We help design policies, build verification processes, support executive‑level training, and develop incident response plans that focus on behavior and accountability. Our services enable leaders to strengthen cybersecurity from the top down, creating protection that supports the business, clients, and long‑term peace of mind.