Data Protection as a Strategic Business Priority
Data protection is no longer simply an IT concern—it has become a business-critical necessity. Safeguarding sensitive information now means protecting customer trust, staying compliant with laws, and securing long-term growth. Organizations that overlook compliance face regulatory fines, financial penalties, and long-lasting damage to their reputation.
For small and medium-sized businesses (SMBs), the risks are amplified. With fewer staff, smaller budgets, and increasing regulatory complexity, achieving compliance is often difficult. This is why the role of technology executives—CIOs, CTOs, and IT directors—has never been more vital. They must build strategies that balance cost efficiency with strong, lasting protection.
At Gallop Technology Group, we help businesses simplify compliance while strengthening security. Our Free Domain Security Check Up uncovers hidden risks, while our tailored cybersecurity services deliver reliable, affordable protection designed for everyone. With the right support, IT leaders can turn compliance into a competitive strength rather than a constant struggle.
The Pivotal Role of IT Leaders in Data Security
IT executives play a central role in managing both compliance and protection. Their responsibilities go far beyond running systems or troubleshooting networks. They must identify risks, allocate resources, and build an environment where every employee understands the importance of data protection.
Strong IT leadership ensures compliance is part of company culture, not just a box-ticking exercise. Done well, it reduces risk exposure, builds trust with clients, and aligns the business with regulatory expectations.
Core Challenges to Data Protection Compliance
Limited Awareness Among Employees and Leaders
A major barrier to compliance is the false belief that only large corporations face cyber threats. Many employees—and sometimes executives—do not realize that SMBs are frequently targeted because of weaker defenses. This lack of awareness leads to careless mistakes, like poor password practices or ignoring security protocols.
IT leaders can change this by:
- Rolling out security awareness campaigns that share real-world examples.
- Running phishing tests to highlight risks in a practical way.
- Holding mandatory workshops on compliance policies and safe practices.
When employees are continuously reminded of the stakes, data protection compliance becomes part of daily behavior.
Tight Budgets and Resource Shortages
Financial constraints are among the biggest obstacles SMBs face. Many businesses delay investing in data security tools, prioritizing revenue projects instead. Unfortunately, the cost of a single breach often far exceeds the expense of preventative measures.
CIOs and CTOs can push for smarter funding by:
- Presenting comparisons between compliance investments and breach recovery costs.
- Leveraging affordable cloud platforms with built-in compliance features.
- Automating monitoring and reporting tasks to reduce manual workloads.
Framing compliance as risk reduction and cost savings helps businesses treat it as an investment rather than a burden.
Overburdened Internal IT Staff
Many organizations expect their small IT teams to manage everything—from system upkeep to regulatory compliance. With the speed at which cyber risks evolve, this expectation is unrealistic.
To relieve pressure, IT leaders should:
- Provide continuous training and certification opportunities.
- Partner with trusted external providers, such as Gallop Technology Group, for advanced protection.
- Adopt automation tools that simplify compliance reporting and monitoring.
This hybrid approach allows internal teams to focus on core business operations while still maintaining strong data protection.
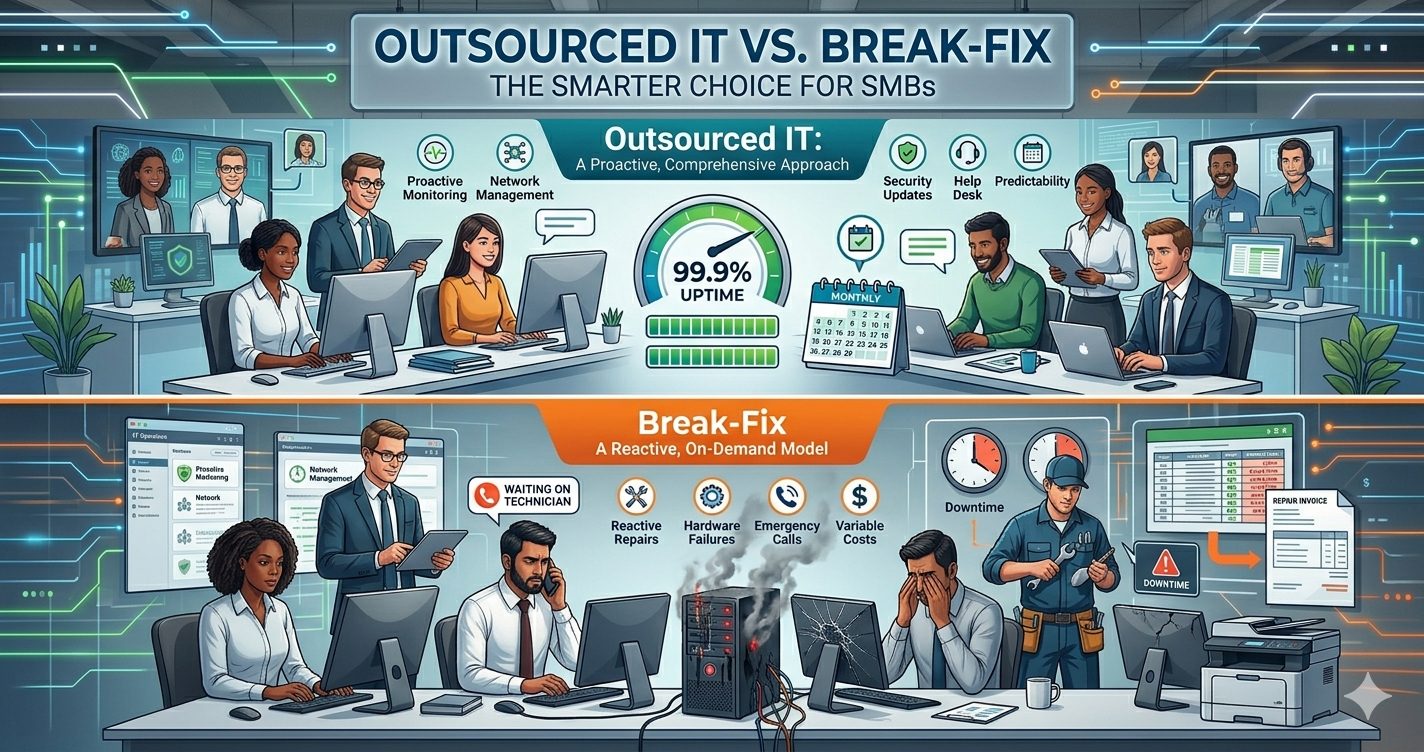
Outsourcing Without Proper Oversight
Outsourcing IT services is common, but handing over responsibilities without clear oversight can create major gaps. Some Managed Service Providers (MSPs) lack expertise in compliance and data loss prevention, which may expose businesses to risks.
To avoid these issues, IT executives should:
- Perform thorough vetting of external vendors, including certifications and references.
- Clearly define contractual obligations around data handling and compliance.
- Conduct ongoing audits to ensure providers meet required standards.
When outsourcing is managed properly, it strengthens compliance rather than weakening it.
Complex Regulatory Requirements
One of the most overwhelming aspects of compliance is the variety of rules across industries and regions. Healthcare providers must meet HIPAA standards, financial institutions must comply with PCI DSS, and businesses serving European clients must adhere to GDPR.
To manage this complexity, IT leaders can:
- Establish compliance playbooks specific to their industry.
- Deploy tools that automatically track and document compliance tasks.
- Seek outside expertise to ensure they meet standards without unnecessary risk.
A structured approach keeps businesses aligned with legal requirements while avoiding confusion.
Disruptions During Security Rollouts
Introducing stronger security protocols often disrupts daily operations. Employees may resist new systems that appear to slow them down, such as stricter logins or limited access.
To ease the transition, IT leaders should:
- Introduce changes in phases rather than all at once.
- Clearly explain how these measures benefit the business long term.
- Provide training and live support during the rollout process.
With strong communication, compliance upgrades can be integrated smoothly without derailing productivity.
Human Error as an Ongoing Risk
No matter how strong the defenses, human mistakes remain a major cause of breaches. Clicking on phishing links, reusing weak passwords, or mishandling confidential files can all expose an organization to threats.
IT leaders can reduce this risk through:
- Enforcing multi-factor authentication (MFA) and password security standards.
- Establishing clear reporting channels for suspicious incidents.
- Providing regular refresher training to keep employees alert.
When employees are both trained and accountable, data protection compliance becomes much stronger.

Strategies to Strengthen Data Protection
Creating a Security-First Company Culture
Compliance is not sustainable if it’s viewed as an annual checklist. It must be part of company culture. IT leaders can:
- Recognize employees who consistently follow data security best practices.
- Include security expectations during onboarding.
- Lead by example—executives must model good security behaviors themselves.
A culture that prioritizes compliance ensures long-term resilience.
Technology as a Compliance Enabler
Modern technology offers powerful ways to support compliance, including:
- Data Loss Prevention (DLP) tools to monitor and prevent unauthorized sharing.
- Encryption for both stored and transmitted information.
- Identity and Access Management (IAM) to control permissions.
- SIEM solutions that centralize threat monitoring and automate compliance reporting.
The best results come from combining tools that align with business size, industry, and regulations.
Incident Response and Preparedness
Even the best-protected systems can experience breaches. This makes incident response planning a compliance essential. IT leaders should:
- Develop incident response guides with clear step-by-step instructions.
- Assign roles and responsibilities to avoid confusion in a crisis.
- Run simulation drills to test how prepared teams really are.
Having a plan shows regulators and clients that the business takes data protection compliance seriously.
Ongoing Monitoring and Improvement
Threats evolve and regulations change frequently. Businesses cannot afford to “set it and forget it.” IT leaders must:
- Conduct quarterly compliance reviews.
- Track updates in regulations relevant to their industry.
- Use dashboards to gain real-time visibility into compliance health.
This approach ensures that compliance stays up to date and effective over time.
Protect Your Business with Expert Support
Maintaining data protection compliance is difficult, but it’s also essential for customer trust and sustainable growth. With strong IT leadership, businesses can turn compliance challenges into opportunities for resilience.
At Gallop Technology Group, we support businesses with:
- Free Domain Security Check Ups to uncover hidden vulnerabilities.
- Customized data security and data loss prevention solutions.
- Managed IT and continuous monitoring to stop threats before they impact operations.
Call us today at 480-614-4227 to safeguard your business and strengthen your compliance. With the right partner and a proactive approach, you can master data protection and thrive securely in a digital-first environment.
Source