Maximizing IT Planning with AI: Essential Insights and Strategies
New IT and Cybersecurity Strategy for 2025: A Guide for Office Managers
As we begin 2025, the IT and cybersecurity sectors are progressing at a rapid rate. For office managers, staying ahead of these changes is crucial to ensure the security and efficiency of their organizations. This article outlines a comprehensive IT and cybersecurity strategy tailored for 2025, focusing on the latest trends, technologies, and best practices.
Embracing Artificial Intelligence and Automation
Artificial Intelligence (AI) and automation are no longer futuristic concepts; they are integral to modern IT strategies. In 2025, AI-driven tools are essential for enhancing cybersecurity measures. These tools can detect anomalies, predict potential threats, and automate responses to incidents, significantly reducing the time and effort required to manage security.
For office managers, integrating AI into your IT infrastructure means investing in AI-powered security solutions. These solutions can monitor network traffic, identify suspicious activities, and even respond to threats in real-time. Additionally, AI can help in managing routine tasks such as software updates and patch management, freeing up your IT team to focus on more strategic initiatives.
Strengthening Endpoint Security
With the rise of remote work and the proliferation of mobile devices, endpoint security has become a critical concern. In 2025, ensuring that all endpoints—laptops, smartphones, tablets, and IoT devices—are secure is paramount. Implementing robust endpoint protection platforms (EPP) and endpoint detection and response (EDR) solutions can help safeguard these devices against malware, ransomware, and other cyber threats.
Office managers should prioritize deploying comprehensive endpoint security solutions that offer real-time monitoring, threat detection, and automated response capabilities. Regularly updating and patching all devices is also essential to protect against vulnerabilities.
Adopting Zero Trust Architecture
The Zero Trust model, which operates on the principle of “never trust, always verify,” is gaining traction as a fundamental cybersecurity strategy. In 2025, adopting a Zero Trust architecture means continuously verifying the identity and integrity of every user and device attempting to access your network.
For office managers, implementing Zero Trust involves several key steps:
1. Segmenting the Network: Divide your network into smaller, isolated segments to limit the spread of potential breaches.
2. Multi-Factor Authentication (MFA): Enforce MFA for all users to add an extra layer of security.
3. Continuous Monitoring: Use advanced monitoring tools to track user activities and detect any unusual behavior.
4. Least Privilege Access: Ensure that users have only the minimum access necessary to perform their tasks.
Enhancing Data Protection and Privacy
Data protection and privacy are more critical than ever, especially with increasing regulatory requirements such as GDPR and CCPA. In 2025, office managers must ensure that their organizations comply with these regulations and protect sensitive data from breaches.
Key strategies for enhancing data protection include:
● Data Encryption: To prevent unauthorized access, ensure data is encrypted both at rest and while in transit.
● Data Loss Prevention (DLP): Implement DLP solutions to monitor and control data transfers, ensuring that sensitive information does not leave the organization.
● Regular Audits: Conduct regular audits to identify and address potential vulnerabilities in your data protection measures.
Leveraging Cloud Security
The adoption of cloud services continues to grow, offering flexibility and scalability for businesses. However, cloud security remains a top concern. In 2025, office managers must ensure that their cloud environments are secure and compliant with industry standards.
To enhance cloud security, consider the following:
● Cloud Access Security Brokers (CASBs): Use CASBs to monitor and control access to cloud services, ensuring that data is protected.
● Secure Configuration: Ensure that cloud services are configured securely, following best practices and guidelines.
● Regular Assessments: Conduct regular security assessments and penetration testing to identify and mitigate potential risks.
Fostering a Cybersecurity Culture
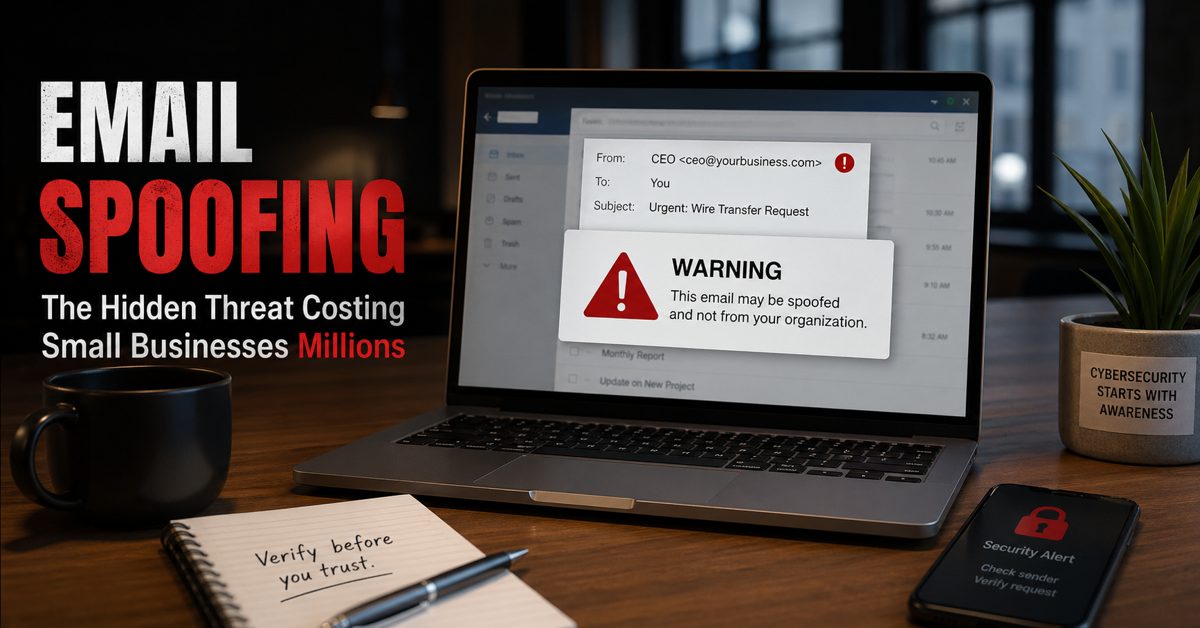
A strong cybersecurity culture is essential for protecting your organization against threats. In 2025, office managers should focus on fostering a culture of security awareness and responsibility among employees.
Key initiatives to promote a cybersecurity culture include:
● Training and Education: Provide regular training sessions to educate employees about the latest threats and best practices for staying secure.
● Phishing Simulations: Conduct phishing simulations to test employees’ awareness and response to phishing attacks.
● Clear Policies and Procedures: Establish clear cybersecurity policies and procedures, and ensure that all employees understand and follow them.
Preparing for Emerging Threats
Cybersecurity is in a state of constant evolution, with new threats emerging on a regular basis. In 2025, office managers must stay informed about the latest trends and threats to effectively protect their organizations.
Some emerging threats to watch out for include:
● Deepfakes: The use of AI to create realistic but fake videos and audio recordings poses a significant threat to organizations.
● Quantum Computing: As quantum computing advances, it could potentially break current encryption methods, necessitating the adoption of quantum-resistant algorithms.
● Supply Chain Attacks: Cybercriminals are more frequently targeting supply chains to infiltrate larger networks. Securing third-party vendors and suppliers is essential.
Conclusion
As we navigate the complexities of 2025, a robust IT and cybersecurity strategy is essential for office managers to protect their organizations. By embracing AI and automation, strengthening endpoint security, adopting Zero Trust architecture, enhancing data protection, leveraging cloud security, fostering a cybersecurity culture, and preparing for emerging threats, office managers can ensure that their organizations remain secure and resilient in the face of evolving cyber threats.
Staying proactive and informed is key to navigating the ever-changing cybersecurity landscape. By implementing these strategies, office managers can play a pivotal role in safeguarding their organizations and ensuring a secure future.
Source: Forbes.com, Dig-in.com