Small Businesses for a Modern Cybersecurity Approach
The digital landscape continues to evolve, bringing both opportunities and threats for small business owners. Technology is no longer just a support function—it is a critical enabler of growth and innovation. However, with the rise of sophisticated cyberattacks and increasing reliance on digital tools, small business owners must adopt a forward-thinking cybersecurity approach to stay competitive and protected.
At Gallop Technology Group, we empower small businesses with tailored IT solutions, including domain security checkups and advanced cybersecurity services. With the right strategy, small businesses can protect sensitive data, ensure compliance, and confidently use technology as a driver of growth.
Below, we explore the 10 essentials of a robust cybersecurity approach that small business owners should prioritize in 2025.
Understanding the Modern Cyber Threat Landscape
Cyber threats are no longer limited to large enterprises. Small businesses face the same dangers but often with fewer defenses in place. Hackers see them as easy entry points into bigger networks or as sources of sensitive financial data.
Some of the most common attacks targeting small businesses include:
- Phishing scams: Deceptive emails or texts designed to steal credentials.
- Ransomware: Malicious software that locks systems until a ransom is paid.
- Data breaches: Unauthorized access to customer or financial information.
In 2025, cybercriminals are using automation and AI-driven attacks, which means that even businesses with modest digital footprints can be targeted. For small business owners, awareness and vigilance are the first layers of defense. A strong cybersecurity approach begins with recognizing that the risks are real—and preparing accordingly.
Building a Resilient IT Infrastructure
A resilient IT infrastructure acts as the backbone of every business. Without it, even the best security policies will fall short. Small businesses should focus on making their IT environment adaptable and secure.
Key steps include:
- Adopting Cloud Solutions: Cloud platforms often provide built-in protections like encryption and automatic patching. They are usually safer than relying on outdated, on-premises servers.
- Regular Software Updates: Outdated systems are prime targets for hackers. Automatic updates across devices help close vulnerabilities.
- Backup and Recovery Systems: Automated daily backups, preferably to both cloud and offline storage, ensure critical data is safe from loss or ransomware.
- Network Segmentation: Separating guest Wi-Fi from internal business networks minimizes exposure.
Investing in infrastructure may seem costly upfront, but it boosts efficiency, strengthens cyber security for small businesses, and ensures scalability as the business grows.
Employee Training and Cybersecurity Awareness
Employees are often the weakest—and strongest—link in cybersecurity. Without training, they can fall victim to scams. With the right education, they become the business’s first defense line.
Training should cover:
- Identifying suspicious emails and links.
- Creating and managing strong passwords.
- Safe use of public Wi-Fi and remote work tools.
- How to report suspicious activity quickly.
According to industry reports, more than 80% of breaches involve human error. By implementing ongoing training and including cybersecurity best practices in onboarding, businesses drastically reduce their risk exposure. Even short monthly refreshers or phishing simulations can help employees stay alert.
Enforcing Strong Access Controls
Access control prevents unauthorized users from reaching sensitive systems. The goal is to ensure that employees can only access what they need for their roles.
For example:
- An office manager may need access to scheduling software but not payroll records.
- A legal assistant may need access to case files but not client billing data.
Practical approaches include role-based access controls (RBAC), password management tools, and account monitoring. By limiting access, small businesses reduce the number of entry points cybercriminals can exploit.
Multi-Factor Authentication (MFA)
Passwords alone are not enough. Many small businesses have already experienced breaches caused by stolen or weak passwords. Multi-factor authentication adds a second layer, such as a code sent to a mobile phone, an authenticator app, or biometric verification.
MFA is now considered a minimum standard in cybersecurity services. Businesses that adopt MFA dramatically reduce their risk of unauthorized access. With many low-cost or free MFA options available, there is no reason SMBs should operate without it.
Endpoint Security for Remote Workforces
With hybrid work here to stay, endpoints are now among the most vulnerable parts of a network. Laptops, smartphones, and tablets used outside the office may not have the same protections as in-house devices.
Best practices include:
- Installing antivirus software and firewalls.
- Using device management systems to monitor and secure hardware.
- Enforce policies that require employees to lock devices and use secure Wi-Fi connections.
Protecting endpoints ensures business continuity regardless of where employees are working. Without these measures, even one lost or stolen device can put the entire business at risk.
Establishing an Incident Response Plan
Preparation matters. Businesses without a response plan often panic during a breach, making costly mistakes. An incident response plan outlines exactly what steps to take when an attack occurs.
The plan should include:
- Containment steps (isolating affected systems).
- Notification protocols for employees, customers, and regulators.
- Procedures for restoring backups and systems.
- Post-incident review to strengthen defenses.
Having a plan reduces downtime, maintains trust, and ensures compliance with legal requirements. Even small businesses should rehearse response scenarios at least once a year.
Leveraging Affordable Cybersecurity Tools and Services
Many small businesses hesitate to invest in cybersecurity, assuming it’s too expensive. The reality is that affordable solutions are widely available.
Options include:
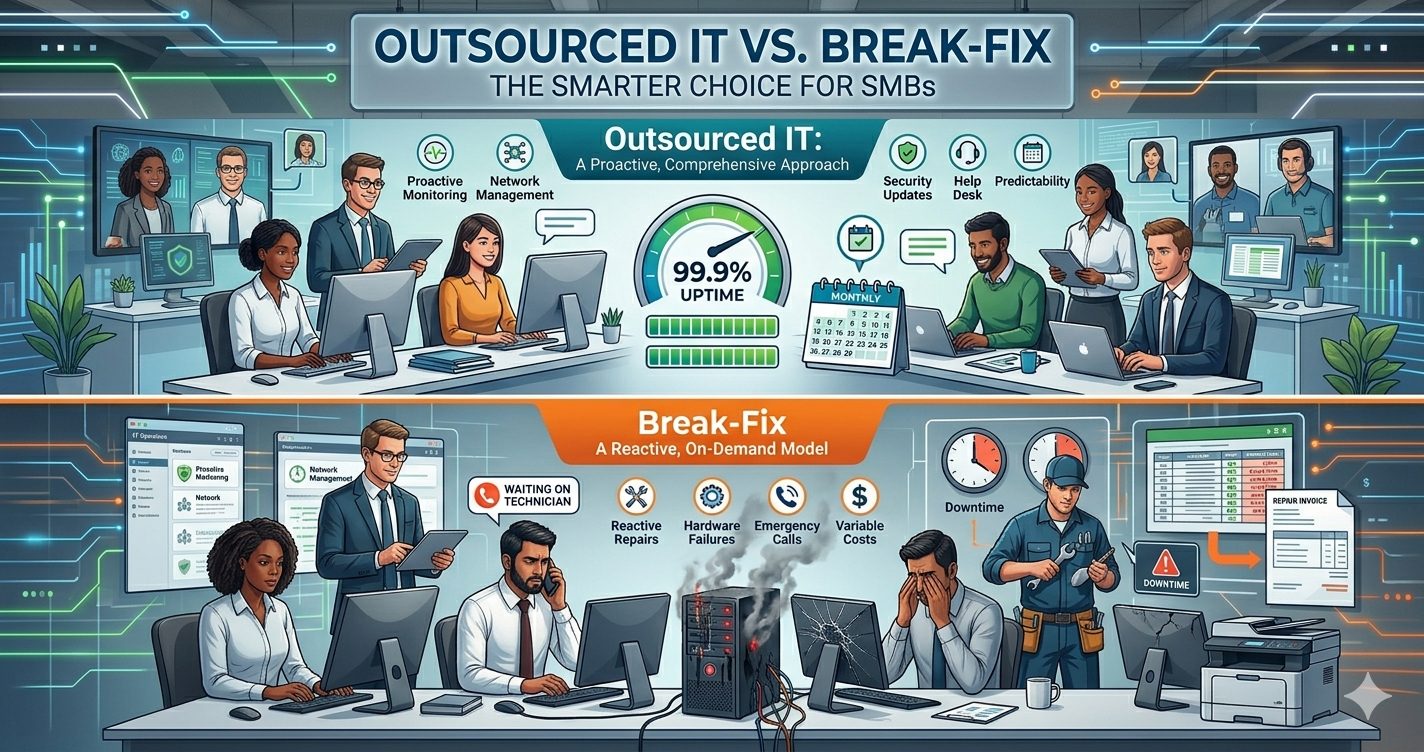
- Managed IT Services: Outsourcing to experts gives small businesses enterprise-level protection without hiring a full team.
- Unified Threat Management (UTM): Combines firewalls, VPNs, and intrusion detection in one easy-to-manage solution.
- Free Tools: Reputable companies often offer free antivirus, basic vulnerability scans, and even limited monitoring services.
By strategically using these resources, small businesses can strengthen their cybersecurity approach while staying within budget.
Compliance and Legal Considerations
Regulatory compliance is no longer optional. Laws such as GDPR in Europe and CCPA in California are enforcing strict requirements on data collection, storage, and usage. Non-compliance can result in heavy fines and reputational damage.
Small businesses must:
- Encrypt sensitive data like customer payment details.
- Store records securely and restrict access.
- Establish clear policies for how data is collected, shared, and deleted.
- Regularly review updates to state and federal laws.
By aligning cybersecurity with compliance requirements, small businesses protect both themselves and their customers.
Leadership and a Security-First Culture
Cybersecurity is not just an IT issue—it is a business leadership responsibility. Owners must set the tone by prioritizing security in their decision-making.
Leaders can show commitment by:
- Allocating budget specifically for cybersecurity.
- Staying updated on evolving threats.
- Promoting a security-first culture where employees understand its importance.
When leaders demonstrate commitment, employees are more likely to follow suit. This culture of vigilance creates a business that is resilient, adaptable, and trustworthy.

Partner with Gallop Technology Group for SMB Cybersecurity Success
As 2025 unfolds, small business owners face a critical choice: remain vulnerable to growing cyber threats or embrace a strong, proactive cybersecurity approach. By implementing these 10 cybersecurity best practices, SMBs can protect their data, strengthen customer trust, and unlock new opportunities for growth.
At Gallop Technology Group, we specialize in supporting small businesses with tailored IT and cyber security services. From free domain security checkups to managed IT support, compliance solutions, and proactive monitoring, our team ensures your business is both protected and future-ready. Contact us today at 480-614-4227 to secure your business and thrive in 2025 and beyond.
Source:
- Small Business Administration – Cybersecurity for Small Businesses: https://www.sba.gov/business-guide/manage-your-business/cybersecurity-small-business