Handling Third-Party Vendor Breaches: A Comprehensive Guide
13 Strategies to Make Your Cybersecurity Fail Proof
A cybersecurity strategy is a plan that outlines the steps to manage and protect the company against cyber threats. It includes information security, physical security, and technology.
An information security strategy involves protecting data by limiting access to sensitive data and implementing strong password policies. It also includes encrypting sensitive data on mobile devices, backing up data regularly, and monitoring systems for potential vulnerabilities that can be exploited by hackers.
A physical security strategy involves protecting employees from unauthorized entry into buildings or offices by using locks, cameras, alarms, and other deterrents. It also includes keeping vital information in secure locations such as vaults.
13 Strategies to Keep Your Business Cyber secure
It is important to keep your business cybersecure. Here are some of the most important tips that you can use to avoid online security threats.
1. Make sure that your website has a secure HTTPS connection.
A secure URL should begin with “https” rather than “http.” The “s” in “https” stands for secure, which indicates that the site is using a Secure Sockets Layer (SSL) Certificate.
2. Keep your software updated and patched.
Keeping your software updated and patched is a good way to keep your computer safe from hackers and other cybercriminals. It also helps fix bugs and glitches that might occur in the software for new features.
3. Use two-factor authentication for all your accounts.
Two-factor authentication is a way to protect your accounts and data from hackers.
The first step to protecting your account is enabling two-factor authentication. This means that when you sign in, you’ll need both your password and a one-time code sent to your phone. Even if someone has access to your email account, they won’t be able to get into your account without the one-time code.
This will prevent hackers from accessing any of the information stored on the account in case they manage to get through the password security system.
4. If you need to share sensitive information, don’t use email, text messages or phone calls – use encrypted messaging apps like Signal or WhatsApp.
There are many benefits of using encrypted messaging apps. First, they protect your data from being stolen. Second, they ensure that you can only send messages to the intended recipient. Third, they can be used on multiple devices. Fourth, they allow you to set a timer on messages so that they expire after a certain time period.
Encrypted messaging apps are often used by professionals such as lawyers and doctors who need to share sensitive information with their clients or colleagues without compromising privacy or violating any regulations.
5. Change passwords regularly and make sure they are complex enough to be difficult for hackers to crack.
Passwords are the most common form of authentication for websites and online accounts. In order to protect your account, you need to make sure that your password is strong enough to be difficult for hackers to crack.
A strong password can be a mixture of letters, numbers, and symbols. It should not contain personal information or words that can be found in the dictionary. You should also change passwords regularly and make sure that you have different passwords for each account.
6. Don’t store sensitive information in public cloud storage services like Dropbox or OneDrive – these are not as secure as local hard drives and require a lot of effort on the part of the user.
Public cloud storage services like Dropbox or OneDrive are not as secure as local storage. They offer limited protection and can be accessed by unauthorized parties. It is better to use a service that offers end-to-end encryption like Box, iCloud, Google Drive, etc.
7. Make sure you have antivirus.
An antivirus is a software that protects your computer or laptop from viruses, malware, and other types of malicious software.
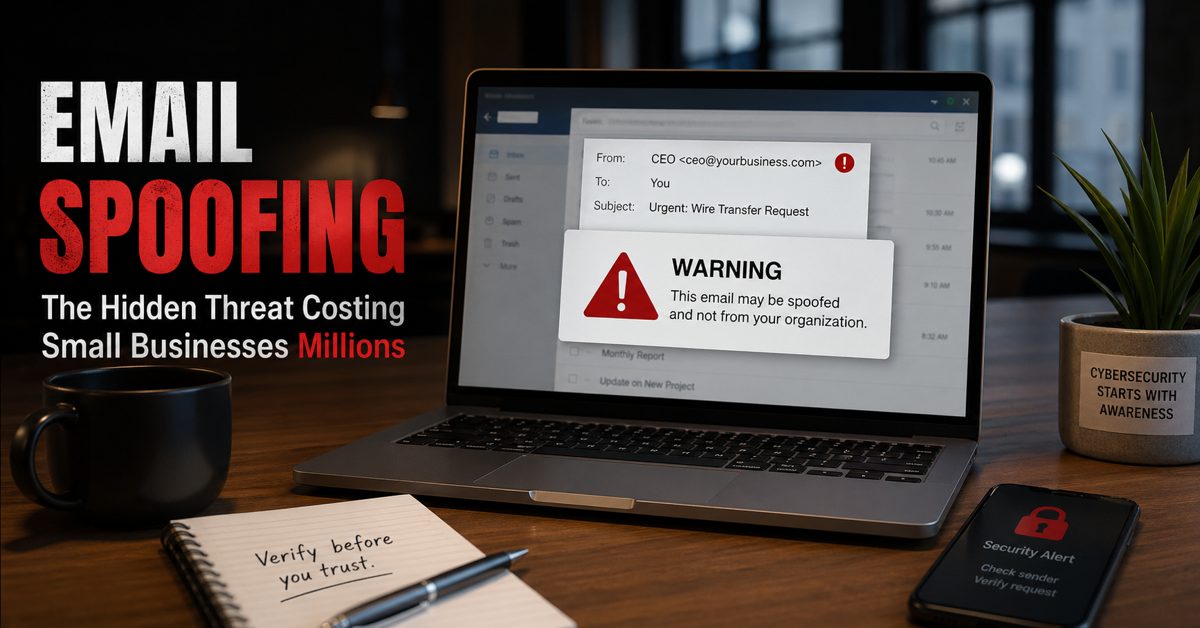
8. Watch out for phishing scams.
Anti-spyware and firewall settings should be used to prevent phishing attacks and users should update the programs regularly. Firewall protection prevents access to malicious files by blocking the attacks. Antivirus software scans every file which comes through the Internet to your computer.
9. Make sure that employees are trained in how to spot suspicious emails.
A company should make sure that their employees are trained in how to spot suspicious emails. A lot of phishing emails are sent out every day, and a lot of people fall victim to them. This is because they don’t know what to look for in an email.
Phishing emails are often used by hackers as a way to steal personal information from unsuspecting people. They send out an email that looks legitimate, but when the person clicks on it, it takes them to a site where they can enter their personal information and then the hacker will have access to it.
If someone were to see an email like this, they should hover over the link in the email and see if there is an address listed there before clicking on it. If not, then they should not click on it.
10. Keep a close eye on what’s happening on your website and social media profiles.
With the increasing popularity of social media and the internet, it is becoming easier for people to find content that they are looking for. And this includes your content as well.
Keeping a close eye on what’s happening on your website and social media profiles is a good way to make sure that you are not missing any opportunities to engage with your audience.
11. Be careful with what you share online.
Before sharing information online, consider what you are sharing (how sensitive the information is) and who you want to share the information with. If the information is general in nature or restricted to a site that isn’t available to the general public, there should be little risk in sharing it.
12. Create a privacy policy.
Write your Privacy Policy in simple, straightforward language. Regularly update your policy to reflect changes in the law, your business, or your protocols. Notify users of these updates, and include the policy’s effective date. Maintain transparency and your commitment to user privacy.
13. Use encryption tools.
When companies use encryption tools, they can protect their sensitive data from unauthorized access.
Encryption is a process of converting data into a code so that it cannot be read by anyone who does not have the key to decrypt it. There are various types of encryption tools available for businesses.
Best Practices for Protecting Against Ransomware and Other Malware Attacks
Best practices for protecting against malware attacks include backing up your data on an external hard drive or USB drive as well as updating your operating system regularly. You should also install anti-virus software on every device you have in order to prevent infections from spreading throughout your home or office network.
Keep your Cybersecurity in Check Today
It is important for businesses to keep their cybersecurity up-to-date and secure, as cybercriminals are becoming more brazen by the day.
In conclusion, making your cybersecurity fail-proof is a continuous process that requires vigilance and proactive measures. By implementing these strategies, you can significantly reduce the risk of falling victim to cyber threats. In the field of cybersecurity, it’s crucial to understand that taking preventative measures is more effective than trying to fix problems after they occur. Stay safe online!
Source: g5tech.com